
Vpn Autoconnect 115 Download
One of the great benefits deploying Sophos UTM in your home network is the ability to configure a VPN with incredible ease. For those that are unfamiliar, a VPN (stands for Virtual Private Network) enables you to access your home network from anywhere in the world as long as you have an internet connection. This can be useful for many reasons. Here are a few: VPN Benefits • The ability to access internal devices at home without opening up your firewall (Remote Desktop or VNC, for example) • Encrypting your traffic so it cannot be intercepted and manipulated (While in an airport or a coffee shop, for example) • Making your online presence appear in a location other than your current one (Some use this to access Netflix and other services from outside the U.S.) There are many different types of VPNs (IPSec, L2TP over IPSec, PPTP etc), where the difference is encryption patterns. Here I’ll explain how to set up an SSL VPN specifically. SSL VPN Benefits SSL VPNs are not necessarily the most secure of the aforementioned options, but it is more than sufficient for home use.
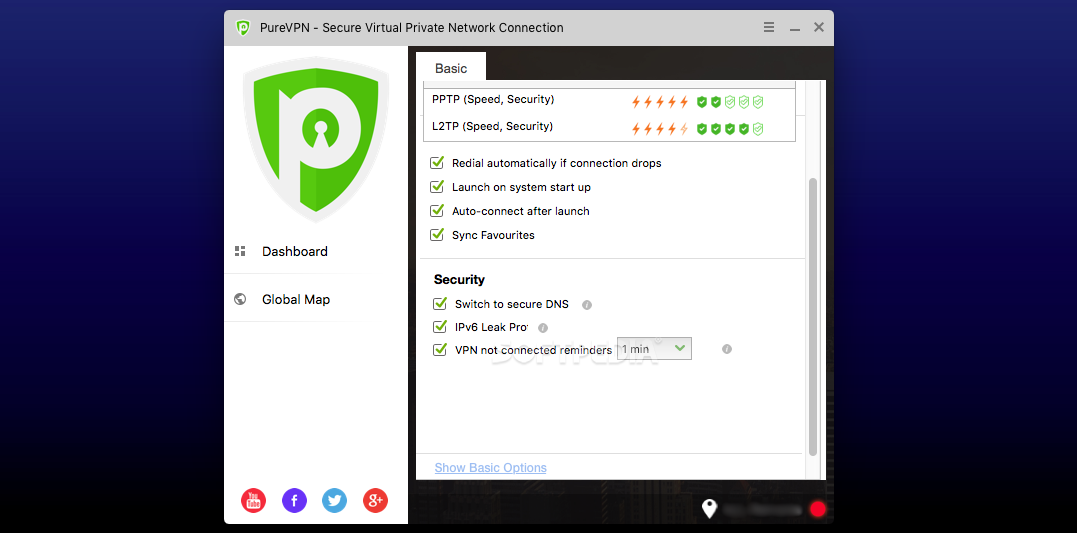
Download vpnautoconnect for free. Vpnautoconnect is a daemon that allow you to reconnect automatically (at startup too) a vpn create with network manager.It can reconnect very quickly and monitor the bandwith, It works with pptp and openvpn connection.
One benefit that makes an SSL VPN especially useful is the convenience of availability. Most VPN encryption protocols require specific ports to be open in order to work. For example, if you’re at work and try to connect to a PPTP VPN, it won’t work because your company has not opened up port 1723 (the port PPTP uses) on their network. Generally, enterprises will not poke holes in their firewall for you to access an external VPN. Chertezhi samoleta h 14a.
Rusi bavshvebis gaupatiureba. SSL VPN uses port 443 for encryption just like all secure websites (those with “http s://” in front of them). The only way to block an SSL VPN is to block port 443, and considering that for secure transfer, it is not likely to be blocked. This guide takes you through setting up a Sophos UTM SSL VPN in 7 simple steps! Set up Users If you haven’t already set up users on your network, you will need to implement at least one. You will use this user to access the User Portal, which will be discussed later.
As you can see, I create two users for this purpose. This simplifies configuration on the client end.
Configure “lanssl” as a user, and “wanssl” as another user. These names will come to make sense in step 2. Configure SSL VPN Here we will configure the actual Sophos UTM SSL VPN service. We will create two profiles where each of the previous two users (lanssl, and wanssl) will be used.